Decompiling Encrypted iOS binaries
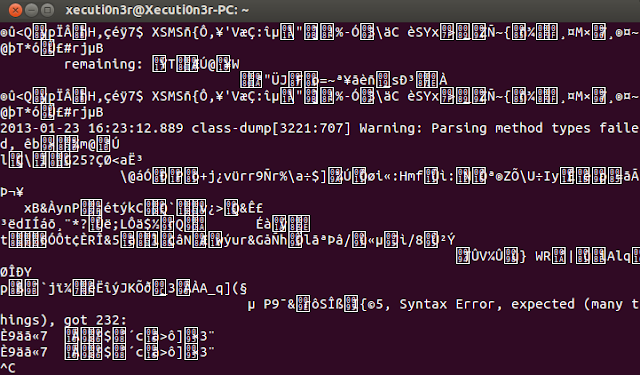
Introduction: In my previous article , i had described how you would normally go about decompiling an iOS application. That method would be working for a majority of applications. However, many a times the developers push in security feature to prevent the attackers from decompiling/debugging the application. In our case, though we are the developers friends and are testing the application, it would be good if we actually follow the same route as an attacker would. That way, we can understand what exact information is disclosed and how the application can be compromised. Requirements: iOS device must be jailbroken. OpenSSH should be installed on the iOS device. SSH Client on your machine. "Class Dump" should be installed on the iOS device via "Cydia" "Cycript" should be installed on the iOS device via "Cydia". Detailed Steps: First we will try and use the same step as used in our previous post to dump the class file information via "class du...
